Karen, you come to mind off and on, especially when I’m try to keep up with what is happening in the wild world of payments, block chain, cryptocurrency, identity, authentication, trust, identification and who knows what else.
One thing is clear. Lot’s of companies are investing significant sums of money in these various “opportunities”. Yet are we, as a society, on the right path?
We could look to Washington DC, and the other capitals around the world, and this same question would apply. But, not to get distracted.
Let’s start with identity and authentication in the digital space
As you may remember, EMV was something I got deeply involved with, both here in the USA and back when we originally conceived of the specification. We the three founding payment associations had one goal – solve for counterfeit. And, when the issuer or country so desired address lost and stolen fraud. Focused on the physical world of commerce, the Point of Sale. Our original goal was simple. Assure global interoperability by defining a global migration path away from the magnetic stripe. We mutually agreed we had to select a technology capable of protecting the physical token, the card, well into the 21st century.
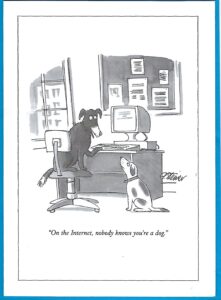
Simultaneously, as was so beautifully captured by the Pete Steiner’s famous 1993 New Yorker cartoon, 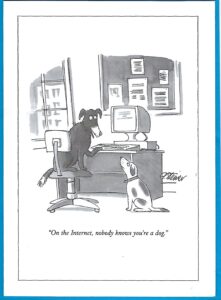 we knew there would be an issue in the digital space, that thing we then call the World Wide Web. MasterCard and Visa set out to define the Secure Electronic Transactions SET, then Visa patented a concept called 3D Secure and more recently worked together with the other owners of EMVCo to create EMV 3D Secure. Each of these, attempts to find a meaningful way of authenticating the cardholder when they paid with a credit or debit card.
we knew there would be an issue in the digital space, that thing we then call the World Wide Web. MasterCard and Visa set out to define the Secure Electronic Transactions SET, then Visa patented a concept called 3D Secure and more recently worked together with the other owners of EMVCo to create EMV 3D Secure. Each of these, attempts to find a meaningful way of authenticating the cardholder when they paid with a credit or debit card.
Today billions of identities have been compromised. The techniques used during an enrollment process online, to verify who you, are no longer viable. Identifiers like our social security number and Person Account Number (PAN), unfortunately, became authenticators, a role they were never designed to support. As EMV was deployed criminal shifted their focus to the Internet and PCI had to be introduced to address the challenges of criminals acquiring payment card and PII data.
As the World Wide Web morphed and grew in value and importance, the potential of monetizing the vast amount of data companies where collected began to scare people; as this recently found comic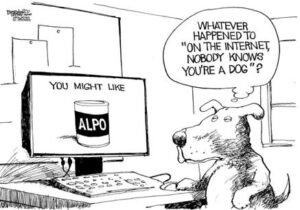 so aptly demonstrates. People, governments and corporations started to struggle with their desire for privacy offset against the value of data corporations are collecting.
so aptly demonstrates. People, governments and corporations started to struggle with their desire for privacy offset against the value of data corporations are collecting.
Way back then, an opportunity to address the issue was offered by Bill Gates. As is always the case, Microsoft the then technical giant wanted something to support what society would ultimately need. The idea of the social good was lost to the value of corporate profit and control.
As the Internet grew to become this marketplace, library, museum, cinema, place to play and place to meet and connect; we imposed well understood enterprise security techniques (username and password) to the consumer space. The password thus became our challenge. How do we convince customers (let alone employees) of the importance of complex, hard to remember passwords – unique to every security conscious relationship we establish on the World Wide Web.
Are biometrics the answer, has the FIDO Alliance and W3C created a set of authentication standards we can all embrace? Hopefully. Unfortunately, most opportunists are seeking to monetize their often proprietary solution, creating what they think is a best of breed consumer experience.
My fear, we are moving from the familiar experience of typing our user name and password; to multiple unique experiences at the front door of each and every web site we seek to log-in to.
As an example my Samsung Android phone has a fingerprint sensor and is FIDO certified. There is a Samsung Pass Authenticator, Microsoft Authenticator, Google Authenticator and several demo versions of various other authenticators. I also receive SMS messages with one time tokens I am asked to enter onto the screen. My PC it also is enabled with a FIDO U2F set of dongles.
Unfortunately my tablet has none of these and assumes I will simply remember, thank you Norton Identity Safe, my various passwords. What a mess we are created all with monetization and the desire to offer a unique consumer experience as the justification.
With all those already installed, I await the introduction of WebAuthN, within the various browsers installed in my PC, tablet and phone.
Moving to Block Chain and Cryptocurrencies
The wild west. The makings of a speculators dream.  The realm of the incomprehensible, built on complex mathematical concepts and the desire to remove the man in the middle and replace them with the miners and nodes distributed around the center. Or, is the idea of the distributed ledger the solution to the challenges of trust in an every expanding universe of connected people and things. One can only wonder?
The realm of the incomprehensible, built on complex mathematical concepts and the desire to remove the man in the middle and replace them with the miners and nodes distributed around the center. Or, is the idea of the distributed ledger the solution to the challenges of trust in an every expanding universe of connected people and things. One can only wonder?
People speak of removing central governments. Yet, they remind us that there is a governing body, book of rules and set of code that is designed to assure immutability. If I understand their, logic we should not trust Governments instead we trust these new open societies and digital enterprises? they speak of removing intermediaries and replace them with nodes and miners. New players responsible for creating and signing the new blocks and distributing it all those who maintain a current copy of the chain.
Is there potential, Absolutely. The challenge is to understand why one would wish to move data from a trusted central repository to a distributed trustless environment. Cost and latency should be part of the discussion and most importantly the level of trust the parties have with each other, identified intermediaries and governing bodies involved in the ecosystem.
Finally Payments
Barter, gold sovereign, IOU, government or bank back notes and coins, checks, cards, account based solutions, digital coins and what next.  Payments have been this ever evolving space. Some seek to monetize the methods businesses, consumers and governments use to pay for the good and services they seek to acquirer, use or explore. Others argue that the cost of payment should not be a source of profit. The interesting twist here is more about the stage an economy is at in their migration from one from of payment to another. Questions of legacy and history limit a markets ability to embrace the new and retire the old.
Payments have been this ever evolving space. Some seek to monetize the methods businesses, consumers and governments use to pay for the good and services they seek to acquirer, use or explore. Others argue that the cost of payment should not be a source of profit. The interesting twist here is more about the stage an economy is at in their migration from one from of payment to another. Questions of legacy and history limit a markets ability to embrace the new and retire the old.
We could shift the conversation and focus on the store of funds: be it the safe in the wall, the checking or savings account at an institutions or digital coins stored in digital memory. We could talk about the entities that focus on the experience and employ the already existing mechanisms. We could think about block chain, crypto currency, identity and authentication.
Does the consumer care? or would we be pleased to simply hear the merchant say thank you for your payment. The frictionless experience of get out of an Uber car or when we click the buy button on Amazon we know the payment will be made and that we will see a receipt in our email. Remove the friction and make sure that only what I owe is paid, that is the experience we seek. We the consumer are not interested in the detail. We just want to know we successfully paid, using the source of funds we set up as our default.
In Conclusion
Yesterday, with this blog incomplete, I listened to The Economist article titled Rousseau, Marx and Nietzsche – The prophets of illiberal progress – Terrible things have been done in their name. What grabbed my attention is that it spoke to the depth of my wider concerns. The article concludes with the following:
The path from illiberal progress to terror is easy to plot. Debate about how to improve the world loses its purpose—because of Marx’s certitude about progress, Rousseau’s pessimism or Nietzsche’s subjectivity. Power accretes—explicitly to economic classes in the thought of Marx and the übermenschen in Nietzsche, and through the subversive manipulation of the general will in Rousseau. And accreted power tramples over the dignity of the individual—because that is what power does.
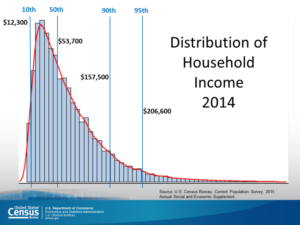
As I think of our capitalist environment, I am concerned and wonder if the publication of the Economist article is timed to educate and alarm. The reality is we are experiencing a concentration of power leading to an increase in the distance between those in the upper 1% and those we call the middle class. Therefore, there is a need to about what is good for the whole, yes a tiny bit of socialism, to restore balance to make sure the wealth and benefits accrue to all and not just the few.
As identification, authentication and payment systems, discussed above, evolves we need to think about the structure of how these solutions will be offered to the market. Are we seeking to address a social issue like crime or terrorism? Are we seeking to improve confidence? Are we attempting to focus on the consumer, citizen and employee needs? Or, is it all about shareholder value and the search for profit?
Like in the article discusses, my fear is Profit will create confusion and complexity. Not more convenient and frictionless experiences.


 . How we restore privacy and what will happen as the new GDPR regulations go into force in Europe, and as California moves to introduce its privacy legislation; requires each of us to watch carefully and be part of the move to restore the consumers’, OUR, right to the data that is us.
. How we restore privacy and what will happen as the new GDPR regulations go into force in Europe, and as California moves to introduce its privacy legislation; requires each of us to watch carefully and be part of the move to restore the consumers’, OUR, right to the data that is us.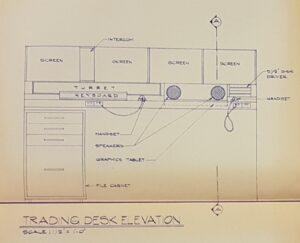
 As these loses escalated, the cost of the various techniques to support more secure authentication have been developed. The market always understood if we could merge a unique object something you Have, with a secret you Know or a biometric something you Are; you would be able to establish a superb form of multi-factor authentication. Many, such as the ICAO, EMV and PIV specifications, embraced the idea of cryptography operating within a secure element or smart card. They further embraced the idea of loading the registered biometric rending into the chip and incorporate the matching algorithm within the software. By then using an external PIN pad or biometric sensor, multi-factor authentication could be enabled. Unfortunately, at considerable cost.
As these loses escalated, the cost of the various techniques to support more secure authentication have been developed. The market always understood if we could merge a unique object something you Have, with a secret you Know or a biometric something you Are; you would be able to establish a superb form of multi-factor authentication. Many, such as the ICAO, EMV and PIV specifications, embraced the idea of cryptography operating within a secure element or smart card. They further embraced the idea of loading the registered biometric rending into the chip and incorporate the matching algorithm within the software. By then using an external PIN pad or biometric sensor, multi-factor authentication could be enabled. Unfortunately, at considerable cost. displaying a onetime password as the answer. In some cases, the user had to first enter a PIN then a number displayed on the screen and then type the value displayed on the device into a field in browser window.
displaying a onetime password as the answer. In some cases, the user had to first enter a PIN then a number displayed on the screen and then type the value displayed on the device into a field in browser window. Something you have with a secret, a one-time password, unique to each event.
Something you have with a secret, a one-time password, unique to each event.
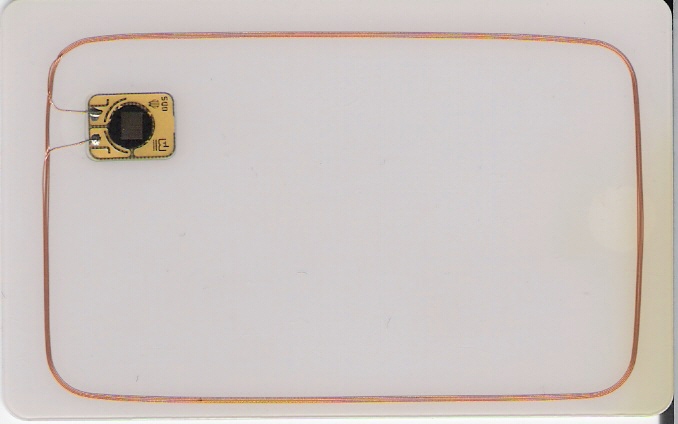
 When we think about the migration to contactless or Dual Interface cards it is important to have a general understanding of what goes into creating the card and the constraints one has to think about, as they work with their marketing teams to design these cards.
When we think about the migration to contactless or Dual Interface cards it is important to have a general understanding of what goes into creating the card and the constraints one has to think about, as they work with their marketing teams to design these cards.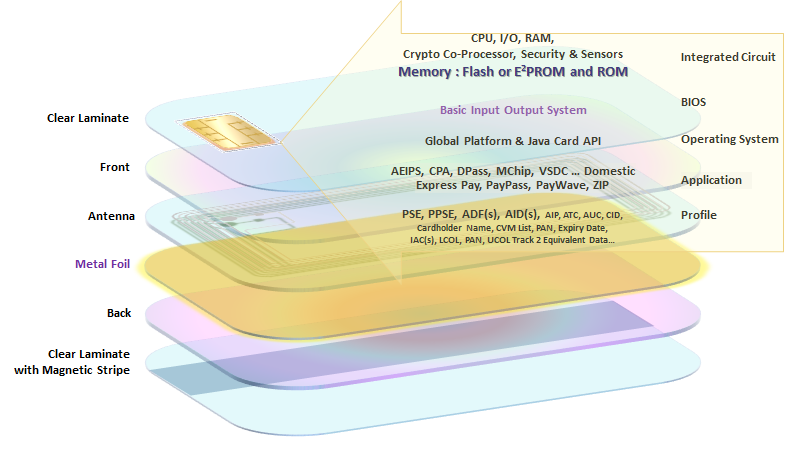
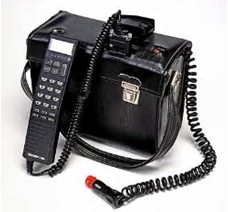 Since 1984, when I was told I needed to carry this mobile phone with me, there has been that nagging issue of needing to make sure it had enough life to get me to the next charge point. My first phone was luck if it could last a half a day so they gave me two, one was always being charged while the other hung on my shoulder. In 1993 while working on the development of the EMV Specifications we focused on the ability to authorize a transaction when the Point of Sale POS device was unwilling or unable to reach the issuer. In 2013 I listened to Visa representatives explain how 100% of all payment transactions could be executed online. Then I ponder getting a
Since 1984, when I was told I needed to carry this mobile phone with me, there has been that nagging issue of needing to make sure it had enough life to get me to the next charge point. My first phone was luck if it could last a half a day so they gave me two, one was always being charged while the other hung on my shoulder. In 1993 while working on the development of the EMV Specifications we focused on the ability to authorize a transaction when the Point of Sale POS device was unwilling or unable to reach the issuer. In 2013 I listened to Visa representatives explain how 100% of all payment transactions could be executed online. Then I ponder getting a  The card remains the essential element of a successful payment transaction.
The card remains the essential element of a successful payment transaction.



 . At this stage in the work of EMV the discussion had turned to the confusion the multiple contactless kernels was creating in the market and more importantly the challenges we would face as the external threats increased demanding that the length of the RSA keys increase accordingly. Ultimately we collectively determined the best course of action was to begin the work on what began know as “Next Gen”. From the beginning it was well understood the migration from where we are today to the “Next Gen” technology solution
. At this stage in the work of EMV the discussion had turned to the confusion the multiple contactless kernels was creating in the market and more importantly the challenges we would face as the external threats increased demanding that the length of the RSA keys increase accordingly. Ultimately we collectively determined the best course of action was to begin the work on what began know as “Next Gen”. From the beginning it was well understood the migration from where we are today to the “Next Gen” technology solution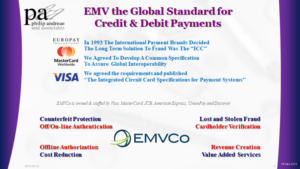
 we knew there would be an issue in the digital space, that thing we then call the World Wide Web. MasterCard and Visa set out to define the Secure Electronic Transactions SET, then Visa patented a concept called 3D Secure and more recently worked together with the other owners of EMVCo to create EMV 3D Secure. Each of these, attempts to find a meaningful way of authenticating the cardholder when they paid with a credit or debit card.
we knew there would be an issue in the digital space, that thing we then call the World Wide Web. MasterCard and Visa set out to define the Secure Electronic Transactions SET, then Visa patented a concept called 3D Secure and more recently worked together with the other owners of EMVCo to create EMV 3D Secure. Each of these, attempts to find a meaningful way of authenticating the cardholder when they paid with a credit or debit card.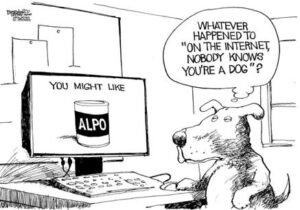 so aptly demonstrates. People, governments and corporations started to struggle with their desire for privacy offset against the value of data corporations are collecting.
so aptly demonstrates. People, governments and corporations started to struggle with their desire for privacy offset against the value of data corporations are collecting. The realm of the incomprehensible, built on complex mathematical concepts and the desire to remove the man in the middle and replace them with the miners and nodes distributed around the center. Or, is the idea of the distributed ledger the solution to the challenges of trust in an every expanding universe of connected people and things. One can only wonder?
The realm of the incomprehensible, built on complex mathematical concepts and the desire to remove the man in the middle and replace them with the miners and nodes distributed around the center. Or, is the idea of the distributed ledger the solution to the challenges of trust in an every expanding universe of connected people and things. One can only wonder? Payments have been this ever evolving space. Some seek to monetize the methods businesses, consumers and governments use to pay for the good and services they seek to acquirer, use or explore. Others argue that the cost of payment should not be a source of profit. The interesting twist here is more about the stage an economy is at in their migration from one from of payment to another. Questions of legacy and history limit a markets ability to embrace the new and retire the old.
Payments have been this ever evolving space. Some seek to monetize the methods businesses, consumers and governments use to pay for the good and services they seek to acquirer, use or explore. Others argue that the cost of payment should not be a source of profit. The interesting twist here is more about the stage an economy is at in their migration from one from of payment to another. Questions of legacy and history limit a markets ability to embrace the new and retire the old.