Category: Business
Reflecting on the year 2020
This morning I am drawn by the press to reflect on who and what we are.
I was glad to read this editorial from one of the various pro-Trump papers. https://nypost.com/2020/12/27/give-it-up-mr-president-for-your-sake-and-the-nations/
It causes me to believe that this nation would be great if “we the people” found common ground and work together to build upon our ancestors’ creation.
We have issues with race and wealth https://www.minneapolisfed.org/events/2021/racism-and-the-economy-focus-on-education.
This discussion of race then leads us to reflect on our history and how the south effectively established segregation as a means of voter suppression. https://www.economist.com/christmas-specials/2020/12/19/reconstruction-reshaped-america-along-lines-contested-today
We distort the truth to satisfy the minds of those in power. Greed and pride are two sins we each must own and work to remove from our evil character.
We must remember, we construct history to serve those who seek to control and influence our young and impressionable children https://twitter.com/pandreae/status/1343923775998455810.
The courts, multiple states Attorney Generals, and those who ran the elections in over 9,000 jurisdictions all agree we worked tirelessly in the face of a pandemic to enable the American citizens’ right to vote. https://www.brennancenter.org/our-work/analysis-opinion/election-lessons-2020
We must respect the people’s decision and stop attempting to claim fraud when no one can convince a court of law and the republican judges appointed by Donald Trump that there was massive voter fraud.
We then must also recognize there was an active attempt to intimate people. https://www.propublica.org/article/pistols-a-hearse-and-trucks-playing-chicken-why-some-voters-felt-harassed-and-intimidated-at-the-polls White men banishing guns carrying Trump flags is the typical image we saw throughout this nation.
And, Today, our President shares his anger with the general public https://twitter.com/realDonaldTrump.
It is time we restore order, accept the will of the people, and work together for the future we all crave.
Where are we in this age of dis-information
It is 11 AM December 6 and I wonder about the past and future of the United States of America. The news is divided. There are those that focus on the Trump-centric right-wing media. There are then those that focus on the Biden-centric left-wing media. The challenge where is the truth. For those capable and willing to watch both sides of the story we may be able to fathom reality. For those fixated on one side or the other, they are no longer are capable of appreciating where the middle of this country lies.
November 3 we had an election and over the next several weeks it became clear that Joe Biden would be our new president. Unfortunately, the current president Donald Trump could not nor would not accept the fact he lost.
In 2016 the popular vote said he lost. Based on how our Constitution is written, the electoral college decided he won. We had to accept this truth and we had to get on with life.
The challenge, since then we have had to live with the lies, the untruths, and the constant cry “fake news”. We had to deal with the constant barrage of POTUS reminding us he is a narcissist, he is the president of the United States, and recognize he was allowed to lie to the public. Is he sane one might ask. Are we?
Digital Identity and Authentic Relationships
When we think of investing in various businesses the goal, of course, is revenue. One of the keys to such success is loyalty. Loyalty is all about the relationship companies create with their customers and the revenue these relationships assure.
If the buyer has something the seller wants, in exchange for the good or service they desire, then a transaction occurs. The challenge is simple, each party defines the value of what they are providing or exchanging and presto the trade occurs.
When society grows and the complexity of what each of us produces and when our needs are not aligned to this process called barter, a means of monetization is established. Society creates a trusted means of exchange – pebbles, coins, money, a promissory note or now even, some would argue, cryptocurrencies.
In other words, society created an answer to enable the exchange of goods and services between parties, who do not have the goods and services the other party seeks.
With cash, coins or other tangible representations of value, commerce is easy. When society does not develop a secure and trusted means of facilitating the exchange of things commerce, innovation and a good life cannot be achieved. To this end, paper money is imbued with ‘value’ based on the integrity of the party issuing the physical or now electronic ‘money’. The addition of the word ‘electronic’ brings technology, computers, and networks into the conversation. One network, typically referred to as the Automated Clearing House ‘ACH’ allows banks to electronic instruct the movement of ‘money from an account at one bank to an account at another.
The addition of the word ‘electronic’ brings technology, computers, and networks into the conversation. One network, typically referred to as the Automated Clearing House ‘ACH’ allows banks to electronic instruct the movement of ‘money from an account at one bank to an account at another. The use of an ach check processing system for business transactions between vendors and customers has become increasingly common in addition to banks. The advantage of this system is that it usually allows businesses to transfer money automatically between bank accounts so that their payments can be cleared out in a short period of time.
In the 1958 Bank of America created Visa Inc., in 1964 the Wallenberg family created Eurocard, and then in 1966 a collection of banks banded together to create the Interbank Card Association, Mastercharge and now MasterCard.
These payment networks, by necessity, add complexity. They create the need to establish a two sided market. On one side the relationship with the buyer, consumer, or cardholder. On the other side if this market the seller, merchant, or retailer.
Issuance and Acceptance. Two words to describe the two sides of a network. It’s only when the two sides of the market have sufficient participants. Only at the tipping point, when critical mass exists, can one claim to have created a self-sustaining network. A network of people promoting use to buyers and a network of merchants willing to accept payment based on the terms and conditions defined by the network. Beginning at this tipping point, the network and it’s Brand blossoms. If either side of the market does not achieve critical mass, the network collapses.
Relationships – The oil of commerce
Any two entities familiar and trusting in the Brand, or each other, can easily establish a temporary relationship with entities associated with the brand. If one or more of the entities require anonymity increases the level of trust and recognition the Brand must establish with these participants.
In a digital environment, we are in need of mechanisms to share and establish trust across trillions of electrons. The two sides of a relationship, in other words, the market, will not take the time to understand or appreciate the need for network and endpoint security; until the risk exceeds a threshold understood by the participants.
The Artifact of Trust
When a mutually trusted set of parties gives the citizen, consumer, employee or courtier a letter, card, device or any uniquely registered object, and provides every acceptor with a reader capable of recognizing the trusted thing. Then the two parties are in a position to establish “trust”. The consumer has a thing which is recognized and trusted by the acceptor. This is often referred to as “What You Have”.
Once the thing is recognized by the acceptor, then, the process of identification and authorizations (the transaction) can take place. The object – the artifact – carries an identifier. It possesses unique characteristics. The object also possesses a means of assuring the acceptor the presentation of that identifier represents a unique representation of that identifier.
The simplest artifact of establishing “trust” is a handheld thing, be it a key, fob, card, watch, pendant, phone, earpiece. It does not matter what it is, all that counts is that the merchant recognizes it and that the consumer is willing to carry and present it.
Trust, for the merchant, means they can, according to defined procedures, recognize and authenticate the thing. They are then in a position to pursue a temporary and trusted relationship. What can be achieved during the time the relationship of trusted is bounded, is constrained by an additional layer. In this layer the consumer, the acceptor and any third parties address which the rights and privileges are to be granted or pursued. This is when the exchange, sale, conversation, tranaction, event or access is granted.
Voting in the age of technology
Voter suppression, voter apathy and voter regret are what we feel, hear and must tolerate.
COVID-19 the corona virus and the ranting of the American President set the stage of an interesting lead up to the November election.
How will we assure the success of the election. We worry about polling places not being open creating very long lines at those polling places we are able to open. We think about Vote by Mail and wonder if some states will even allow those seeking to maintain social distance to request and absentee ballot. Worse still he whose name should not be spoken will accept the results of an election where a significant segment of the population will have taken advantage of the healthier Vote Remote option.
All this said there is another way to enabling the people to express their opinion. We could take advantage of technology. We should ignore those who live in the past and argue technology can never be secured and call this “settled science”. We could bring together the practitioners who are securing technology and ask them to work together to make sure those solutions already pilot tested are as secure as is possible.
Voatz has created a Remote Ballot Marking solution built on the secure foundation of current generation mobile devices. A platform built to mutually authenticate the verified voter is eligible to vote, the device they are using is secure and not infected with malicious software, the communications is encrypted to assure no one can see who the voter decided to vote for, the secure cannot be hacked and each vote is immutable.
All of these security precautions then enhanced with sophisticate detection techniques designed to monitor and make sure those who attempt to attack the system are identified and prosecuted.
Security is inherent in Voatz’s design as is the simplicity of the user interface. A user interface designed to assure everyone, no matter their situation or disability to ability to vote.
Voatz began by focusing on serving our military. People who do not have access to printers, the post office or any other means of casting their ballot. What they do have is a mobile phone and access to the internet. Voatz makes sure they could vote. Voatz then saw an opportunity to serve those with disabilities. With these two constituent solved for Voatz is ready to help each and every America election authority protect your right to vote.
The next step is for you the people to demand the ability to vote. Ask the secretary of state or lieutenant governor to work with Voatz to offer Vote by a Phone as an option this year.
Sunday June 7th 2020
Since early February, we here in the United States have had to live with the coronavirus and its economic implications. Over the last two weeks, we have confronted with the reality of our racist tendencies. Over the last 20+ years, this country has fractured into the left the Democrats and the right the Republicans; groups like the tea party have driven these tribal tendencies who wish to engender their thoughts on everyone.
The sense of discomfort that lives within my soul creates tensions and a sense of despair. If only we could see the light. If only we could believe the truth. If only we could come together as one people each of us would be much happier and able to live a more productive and satisfying life
What can I do? What can you do to change the way we think to change the way we act to change the way we embrace each other? Some would remind us of the works of great religious leaders such as Jesus Christ, Lao-Tzu, Confucius Siddhartha Gautama. Men and I am sure women who have spoken of peace and tranquility. They talked about friendship and the bonds of togetherness? It is these bonds of friendship we have to find again. It is the ability to accept and embrace each other we need to remember. We need to stop arguing with each other. We need to start embracing each other. We need to remember that debate is a good thing, while arguments are not.
When I was a young man, I believed it would take three generations for us to address are the racial tensions in this country. I think my problem then was from which age do we begin; it was not the generation that I came from the baby boomers. Maybe not even Gen X. It needs to have a fresh start. It needs to be built on the beliefs of togetherness. Yesterday evening we watched a documentary about Thurgood Marshall. I had no idea how complexed the arguments and the legal battles have been to reach where we are today. The Jim Crow laws so divisive created the division in the South. Separate but equal established a baseline to segregate those of color from those who believed they had the power.
I so much want to walk forward into a world where peace is the norm where cooperation is how we work together. But, the tension, the tribal tendency, seems to be deeply ingrained in our human psyche. It is the human psyche we need to address. We need to transform our thinking from that of fight and right to that of compassion, cooperation, and solidarity.
What more can I say? I can only pray that ‘we the people’ will find the way forward. That ‘we the people,’ will work together to find a more peaceful union. That we, the people, will finally achieve what the founders envisioned. What some would say God offered us in the Garden of Eden before we fit into the fruit of knowledge. We should harness understanding for good.
Settled science
In March 2020, I moved from the payments industry into the election industry. This movement caused me to wonder about democracy, politics, academia, and the world of technology. What amazed me is how computer science academics could rail at the idea, technology could be used to innovate on the election process. Years ago I imagined participating in a national referendum simply by opening a browser searching for the government website and voting on the measures and contests currently under consideration.
Unfortunately what I’ve learned troubles me. Certain clusters of intelligent individuals believe that they know best. They stigmatize technology and argue that a human being, who writes software, could leave unintended bugs which might lead to unintended consequences. They forget software is an evolutionary science. Through piloting, continuous improvement, testing, and rigorous testing we can eliminate bugs and create stable and secure critically important applications serving our financial, health, national security, and public interests.
Recently in a letter written by verified voting, a nonprofit organization, the word settled science appeared. An intriguing word, an intriguing phrase. I was driven to wonder what did it mean. From my high school years, science was an evolutionary process. A hypothesis was put forward. it was tested. If it was found to be false a new hypothesis was offered, it was tested and on the scientific community went. In one article when googling “Settled Science” I was intrigued to read the word oxymoron followed by an explanation of how if Sir Isaac Newton’s beliefs had been settled science Albert Einstein would never have been able to put forward the concepts of general relativity.
This whole conversation feels very much like a religion, a church, who has a dogmatic belief in the written word of the Bible being the written and only word of God. We forget how man inserts himself into every dialogue. Too often we insert our beliefs on others. Maybe “Settled Science” is the dogmatic belief that we are right and everyone else is wrong.
If this is the case then how do we move forward? If scientists – academics force there will on society than society has lost its objectivity.
The Means of Payment And the Method of Payment
Two words each can be seen as the same as the other. Yet, it is important to create a distinction.
The method of payment should be related to how we execute and not from where the money comes. The means of payment should relate to the source of funds.
Too often, we allow these terms to get lost. Is tapping a payment card at the point of sale or typing in the 16 digits printed or embossed on the card a means of payment? I would argue not! This is the method we use to inform the merchant how they will be paid for the goods and services we seek to procure.
When we talk about the means of payment, we should focus on the source of funds. Are these funds held on deposit, funds in the wallet, or a loan of funds?
Our vocabulary is rich in confusion. These two words in the complex space of payments need to have independents reason.
As an example, I use Apple Pay to pay does not mean Apple is involved in managing the funds. It is simply the method used to share the payment card details with the merchant, enabling the merchant to request funds from the account selected by the user through the Apple Pay user interface.
The Card Was and Is Only a Credential Carrier
Cash is here to stay – cards are the true dinosaurs
This question of the extinction of the payment card is misleading.
What is a payment card? It is the carrier of a set of credentials, A means of Identification offering financial Attributes capable of being authenticated by a party seeking to sell something to the individual or entity presenting the credential as a mechanism to assure payment.
Back when credit cards were designed, the goal was to offer merchants a guarantee of payment and anonymous consumers a means of paying. Behind this means of payment, a financial institution, the issuer, provides the consumer with a “Line of Credit”.
On the merchant side, another financial institution buys these guaranteed receivables from the merchant and charges the merchant a “merchant discount”. Later that day the Issuing Institution advances payment to the Acquiring Institution based on an agreed set of terms and operating rules. Terms and conditions the involved financial institutions collectively agreed upon.
For this method of payment to be effective, a large number of consumers and merchants had to agree to participate; hence the financial institutions came together and formed what we now know as MasterCard and Visa.
Given the state of technology at the time it was essential this new mechanism work without the burden and expense associated with the merchant, supported by the acquirer, contacting the issuer to receive approval, or, in stronger terms be assured of a guarantee of payment. To achieve this result, the merchant needed something to acquire the necessary information to submit a request for payment. For both the merchants and financial institutions,, there had to be a means of authentication. Designed to assure the responsible parties of the authenticity of the person or entity to present their payment credentials.
 To accomplish this goal, just like with money, physical security features are integrated into the payment card designed to allow the merchant to authenticate the uniqueness of the card carrying the payment credential, thus assuring the merchant of the authenticity of the card.
To accomplish this goal, just like with money, physical security features are integrated into the payment card designed to allow the merchant to authenticate the uniqueness of the card carrying the payment credential, thus assuring the merchant of the authenticity of the card.
Overtime criminals successfully counterfeited these security features.
As these features were compromised additional features had to be added.
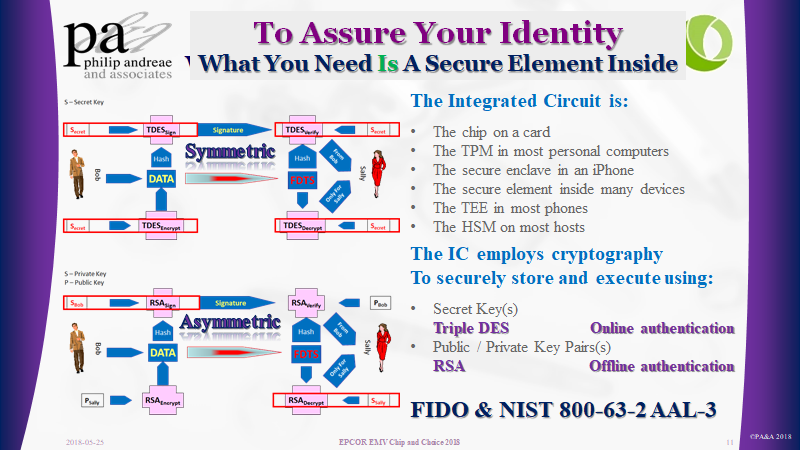
Today, a computer has been embedded inside the card, in order to assure the authenticity of the payment card credentials being presented to the merchant.
These computers embedded onto the front of a payment card exploit the power of cryptography. Cryptographic certificates and digital signatures are created by and for these computers, allowing:
-
- The Issuer (symmetric cryptography) to support Online Authentication
- The merchant (asymmetric cryptography) to support Offline Data Authentication
These two mechanisms prove to the merchant and issuer that the card is unique and the data, credentials, and digital signature it contains or produces are authentic.
Once all the merchants have are capable of reading the data from the chip card, the security features of the card become redundant.
As these features become redundant and the merchants embrace Near Field Communications, based on the ISO 14443 standard, the issuer can replace the card form factor with anything equipped with the necessary computational capabilities and ability to communicate with the terminal over the NFC interface.
This is exactly what Apple Pay and Google Pay have done. They replaced the card with a device. Yes, the Payment Card may become redundant. But, the Payment Credentials they contain, remain.
What we know as card payments, is fundamentally an account-based solution. Money, through the defined settlement process, ultimately move from the line of credit or deposit account of the buyer, through a series of accounts with the participating financial institutions, to the account of the merchant.
Card-based credential payments
simply become
Device-based credential payments
What has this world come to
When we listen to the news, we must think first of the bias of the reporter. This unfortunate truth is troubling in a world where the United States leader speaks of fake news and uses Twitter to stir up the masses. This body of citizens struggles with truth and is easily bent to believe what the leader says.
This particular charismatic leader, like many others in the past, can cause people to believe anything. The challenge, these same people will follow both those with high morals and those without.
Jesus Christ, Siddhartha Gautama, Confucius, Laozi, and a few others spoke wisely and became spiritual leaders many continue to follow.
To name one well remembered, Hitler, like the recent President of this great country, spread lies, and fermented hatred.
How can we rise above when so many are unwilling or unable to see the truth. We must rise above the madness these charismatic immoral individuals ferment.
That is the concern I have felt since first I looked upon the control a church exerts upon the mass.
Cryptocurrency – built on the hopes and dreams of the masses
As is my habit each morning I run through a serious of Google Alerts scanning and reading those that tweak my interest. One of these alerts helps me to stay abreast of what is happening in the crypto market. Most often times the articles present the hype and expectation of those enamored with Bitcoin and the excitement the last ten years of cryptocurrency excitement has wrought.
One article’s conclusion deserves a bit more thought.
5 Costly Tech Mistakes Crypto Beginners Make
There’s a lot of money to be made in cryptocurrency, but it belongs to those who can avoid making ruinous mistakes.
Whether you’re trading or mining, it is important to treat your endeavor with the utmost care and diligence.
As a crypto newcomer, you will go much farther and enjoy success if you note these tech-mistakes and steer clear of them.
This middle sentence once again reinforces my skepticism.
What is behind these immaterial assets?
Is the price of a bitcoin simply the result of the actions of crypto believers, speculators, and gamblers?
Is a cryptocurrencies price driven by the value of the reward required by miners to cover their cost for electric, space and computer resources?
Unlike the US dollar, the British pound, Swiss Franc or other stable country issued currency built on “trust” in the future of the USA, UK or Switzerland; these new currencies are built on peoples’ belief in a speculative and trustless cryptographic universe.
In essence, these cryptocurrencies are built on
The hopes and dreams of many
Behind all of this is the cost of supporting these cryptocurrencies. Costs measured in electric bills and the investment in racks of mining resources “computers”. Is it the ever-increasing need for computation power that drives the ever-increasing need for higher rewards set against the process of halving, apparently designed to address inflation.
This mystery of “inflation” leaves me wondering if inflation of the price a built-in part of a scheme to assure the original and still invested success of the few?
EMVCo Good or Evil
https://www.securepaymentspartnership.com/wp-content/uploads/2019/12/Payment_Insecurity_Final.pdf
In 1993, I was asked by the then CEO of Europay International to establish a relationship with Mastercard, and Visa focused on developing the specifications necessary to assure the interoperability of chip card-based security for credit and debit payment cards. The result published in 1996 was the “EMV Integrated Circuit Card Specifications for Payment Systems.”
From these humble beginnings, EMVCo has emerged as a key organization in managing the standards behind card payment systems. In the white paper Payment Insecurity, commissioned by the Secure Payment Partnership, the author reminds us of the difference between standards managed by an open body and those tightly controlled by an exclusive group of competitors. One wonders if the owners of EMVCo will listen and strive to open up their membership or continue to use this entity to protect their proprietary interests.
In the introduction, the author speaks of a series of questions he intends to address. The first question of the paper
Is EMVCo furthering the entire U.S. payments industry or simply protecting Visa and Mastercard’s market share? page 5
begs the question, why limit the discussion to the USA?
This American only focus is driven by the desires of the Unaffiliated Debit Networks and a set of merchants. The paper ignores fundamental and, yes, anti-competitive elements of the EMV specification – the AID or the Application Identifier. It was and is directly related to the Brand responsible for the underlining technology incorporated into the Chip.
I then read the following complaint and am driven to ask how the consumer interpreted the prior Debit versus Credit prompts.
Visa’s response to this solution was to require merchants to display to consumers a choice between “Visa Debit” and “U.S.
Debit” at checkout. – page 13
In essence, what Visa required was simple, the terminal should comply with the EMV specification for “application selection,” key and inherent in the multi-application design of EMV and the underlining ISO 7816.
Moving further into the document in Section 6.1, the author attempts to document the history leading to the creation of EMVCo. As one of the founding members, the author’s sources were not involved and did not understand the history.
First, only France had a smart card solution designed to address Credit and Debit card fraud. They referred to their implementation as B Zero Prime.
Second, the UK in 1995 was driven by Visa to embrace an earlier version of the Visa specifications adapted to the unique requirements of the UK market and branded UKIS. UKIS and the unique UK requirements are responsible for changing many of the shall’s in the EMV 2.0 version of the specifications to should’s in the EMV 3.0 version. This accommodation was the result of legacy limitation within the X25 network the United Kingdom depended on for card authorizations.
To further identify issues with his record of history, the statement on page 22
EMVCo developed standards for chip cards that could work with credit, debit and stored-value cards
It is fair to suggest EMV attempted to incorporate Stored-Value cards in the specification. But as a result of the competitive realities of Europay’s Clip, Mastercard’s Mondex, and Visa Visa Cash stored value solutions, they agreed to exclude stored value cards from the specifications.
It then goes on to suggest EMV compromised and offered a Signature option. There was not a compromise; it was intentional. The goal, afford the Issuer the ability to determine, by Cardholder, which cardholder verification method they could be configured for. One need was to address issues of the disabled, e.g., the Blind.
Debit Routing as a result of the Durbin amendment. One might wonder why EMV did not consider this idea of multiple networks associated with a card.
EMVCo was unable and unwilling to resolve the lack of a debit AID because EMV was never designed for the U.S. market.
I sense that there is another front coming out of the Debit Networks seeking to argue the anti-competitive nature of EMV. The paper, link below, draws me to wonder about the argumentation surrounding “Application Selection.” Please let’s get back to basics – the “AID=Brand=Payment Scheme” drives “Routing.”
On page 13, it argues consumer confusion. I would argue it ignores the past. The EMV default user prompts of “Visa Debit” and “US Debit” are no more confusing than the historic “Credit,” and “Debit” prompts. I would argue consumer confusion already existed. The EMV specification for Application Selection simply afforded the Issuer the ability to provide more descriptive prompts by employing the “Application Preferred Name” instead of the default “Application Label.”
This whole fight surrounding EMV and Payment Security is really a fight about the future of Card Payments. On one face, they argue the Payment Networks did not assure the security of the card payments to protect revenue. On the other hand, they argue EMVCo is a closed standards organization designed to protect and assure the interests of its shareholders, without consideration for the other stakeholders in the payment, e.g., the merchant.
In the end, the argument comes down to the role, definition, and control. How we structure the underlining payment transaction is what we need to talk about. Who provides the mechanism, guarantee, and support for a particular mechanism decides the rules.
In the Digital world certificates replace so many things
What is a certificate? A certificate as defined by Merriam Webster
certificate noun
1: a document containing a certified statement especially as to the truth of something
specifically: a document certifying that one has fulfilled the requirements of and may practice in a field2: something serving the same end as a certificate
3: a document evidencing ownership or debt
certificate verb
: to testify to or authorize by a certificate
When we designed the EMV specification we employed a cryptographic mechanism to assure the merchant and ultimately the issuer of the presence of a uniquely issued payment card. The goal, address the weakness of the security features then present on a physical payment card.
For the merchant – a local mechanism capable of allowing the device – the point of sale to attest to the membership of that card to the family of cards issued under one of the Payment Network brands.
For the Issuer – a mechanism where the card signed transaction details the merchant would forward a digital certificate – the cryptogram – to the issuer for authentication. This cryptogram included in the message sent to the issuer assured the issuer, the card they issued; was presented to the merchant as a means of payment, for the transaction.
What is a payment card? – It is a certificate, issued by a financial institution, designed to guarantee the merchant will be paid – if they follow the agreed payment brand rules.
What is a ticket? – It is a certificate, issued by the movie theater, or a designated vendor, granting access to some venue or event.
What is a license? – It is a certificate, issued by some authority identifying your right to be or the ability to do something.
In the digital world, certificates are strings of characters, such as 2FG%4T678&b23, created, using some mechanism, by an Authority. The readers, of these characters, use the certificate to Authenticate the uniqueness and Authority associated with the presentation of this certificate by someone or thing to something or someone.
To Identify or to Authenticate what is the difference?
Today I read an article on LinkedIn
‘Identification’ is to give an answer to the question of ‘Who is he/she?’, while ‘Authentication’ is to answer ‘Is he/she the person who he/she claims to be?’
This distinction for me is clear. Yet, based on this article, and personal observation, people do not appreciate the unique difference between these two words.
For those who remember the film War Games, the two young adults were able to access the game simply by learning tidbits about the author of the program. “Joshua” is the critical fact our young hackers unveiled. This single word was both the identifier and the password. A simplistic form of Identification which some may confuse with Authentication.
Our driver’s license number, credit card numbers, passport number, social security number, employee number, email address or other aliases; are identifiers. These values are and should have remained, simple means of linking someone to the person who initially registered on a web site.
We then link these identifiers to a means of Authentication, an Authenticator. We then use the authenticator combined with the identifier to assure Identification. The recent NIST 800-63 standard defines the strength of an Authenticator. The simple reality the authenticator can be a combination of things you know, things you have, and things you are. Combining these factors create different strengths of Authentication.
Back in the day, a password, if properly constructed, was a very strong means of authentication. Unfortunately remembering numerous and unique passwords is unmanageable.
One of the issues we face is how so many entities, companies, and other enterprises have taken the identifier and allowed it to also become a means of Identification, a secret.
As soon as a simple number or string of letters designed as public information, to be shared with others; became a means of Identification we created an untenable situation.
The Surveillance State Exists for Profit
I hope we all understand the data collected on each of us
https://www.nytimes.com/interactive/2019/opinion/internet-privacy-project.html
https://www.nytimes.com/interactive/2019/12/19/opinion/location-tracking-cell-phone.html
As a technologist, the revelation of what is available did not surprise me. I understood how location can easily be captured from all of the electronic devices I use. Be it the GPS chip, the triangulation of Cell Towers or the IP address of the router I am using to access the Internet. Where I am is easily acquired by any application or server I am employing.
What bothered me is that “We the People” have not pushed our governments to regulate the capture and use of this very personal information and data. What bothers me is that most of the citizens of this country or this world do not take the time to read the terms and conditions or the privacy statements provided to us and so often simply consented to them without a thought. And, if they did read them, most of us would not appreciate the language and therefore the meaning of these legal documents.
The surveillance state is real. Marketing companies, employers and so many others are buying the data and using it to improve their delivery of services, advertisements and so much more.
https://www.linkedin.com/pulse/i-hope-we-all-understand-data-collected-each-us-philip-andreae/
Is Identity Dead – The answer is Authentication
Today 2019-12-12 I found my way to the following article and associated podcast.
https://www.constellationr.com/blog-news/identity-dead
Below is a flow of thought as I read and listened. to Jon Reed and linkedin.com/in/lockstep Stephen Wilson discuss this most interesting topic.
Surveillance Capitalism – So many are taking advantage of our data!
We need to evolve through the pony express stage of data management, and get to a point where there are responsible data intermediaries who are being held to account.
Identity management, for me, is about proving things about myself. I want to log onto a bank and prove that I have a particular bank account. Sometimes I want to log on and prove that I am the controller of a multi-party bank account with my wife. And sometimes I want to log onto a health service and prove my health identity. So this is all about proving things about me in different contexts.
In the podcast, they beg the question “Why is the Digital Identity problem still any issue”? This leads one to think about the scale and expectation so many have surrounding this idea of “DIgital Identity”!
They then go on to ask the question What is two-factor authentication and remind us that our phone is a two-factor device, exactly what the standards FIDO Alliance worked to develop. They remind us of the reality that people look after their phones. We know when our phone is not with us.
Why not simply bind my identity to my phone.
Mr. Wilson sees the phone as the second factor. I would suggest our devices, bond to our identity, is the primary factor.
Mr. Wilson reminds us that Identity is all about Verifying Claims. We claim to be someone and the relying party seeks to confirm that I am who I claim to be. Or, when I seek to log back into a website, the relying party needs to make sure it is I – the same person who the relying party originally proofed, registered and agreed on an identifier and an associated means of authentication.
Attributes are more interesting than Identity
Attributes are what matters in the various relationships we have when we interact with another. As we think about our data we need to think seriously about what other parties need to know about us and what we wish to share with them. Efforts in Europe to institute GDPR and the efforts in California to implement CCPA
As I continued to read and follow the thread I ended up at a W3C working group working on “Verifiable Claims” and found the following:
Abstract
We are expecting people to be better than smarter than the crooks. This is an interesting thought that begs the question.
How do “we the people” trust anything we hear, read or otherwise come across.
How does each of us keep up with all of the various products, standards, specifications and other efforts to develop stuff capable of securing our “IDENTITY”?
I am a firm believer in the work the FIDO ALLIANCE and W3C’s work on Web Authentication and recommend its adoption and use based on authenticators capable of adhering to a level of security certification commensurate with the associated risk of the acts, transactions, information, and services offered by the relying party to the user.
Cryptocurrencies, Politics and the Future
A world of volatility and speculation
This morning hash rates, degrees of difficulty and the creating of derivatives to moderate the risk of Bitcoin mining drew me in. Several years ago I was asked to participate in a fireside chat on Crypto-currencies at the Federal Reserve in Atlanta.
One of my concerns then and still today is the exponential growth in the cost of mining. These charts offer a perspective on a concept called the Hash Rate, a measure of the work necessary to create a block.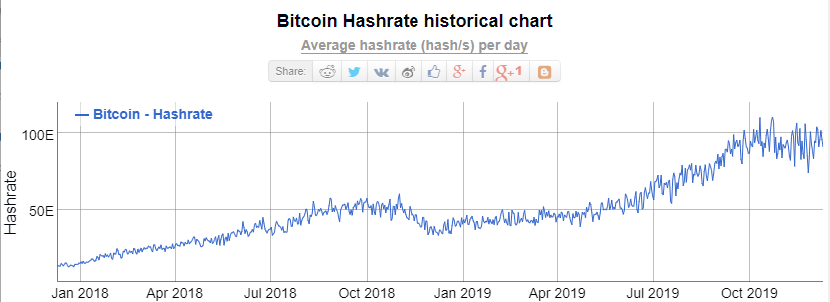 Clearly, as time marches forward, the work to earn the reward gets harder. Thus creating a need to increase the fees charged to add a transaction within a block to the chain.
Clearly, as time marches forward, the work to earn the reward gets harder. Thus creating a need to increase the fees charged to add a transaction within a block to the chain.
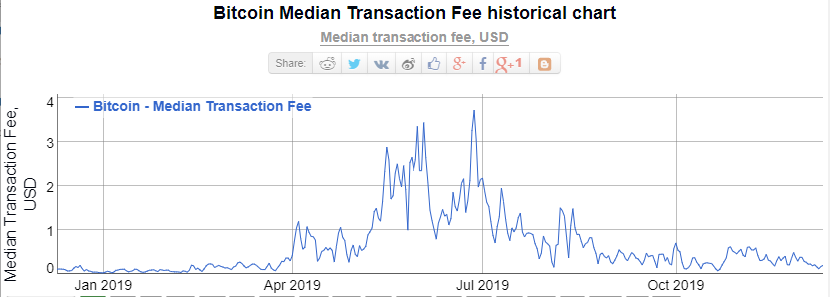 When people speak to the justification of Bitcoin they would speak to the reduction in cost. Is this statement still valid?
When people speak to the justification of Bitcoin they would speak to the reduction in cost. Is this statement still valid?
Disruption, lies, and politics
While considering the potential of Bitcoin; the working of our government rambles on, as we consider the fate of the American President. Lies, bribes, abuse, and obstruction seems to be the order of the day.
The division between political parties; drives division within families, cities, and two people sitting together over lunch creates animosity.
We are now a world driven to speculate or better said gamble while not wanting to find a gentle and graceful road to mutual satisfaction.
We need to reflect consider and potential restore faith in what is real, what is just and what is fair for all.
Spending money on machines of war instead of investing in education and our environment makes no sense to this lone individual. We need to once again seek peace and justice.
Identity – A Most Complex Thought
The idea of my identity, your identity, and our identity took me on a journey into social norms, physical realities, spiritual considerations, psychological consideration, and philosophy. Starting with the classic approach of learning the definition of a word takes us to the dictionary. What then assured the complexity of my quest is each of several definitions is similar, but, not the same.
-
-
- https://www.dictionary.com/browse/identity
- https://www.lexico.com/en/definition/identity
- https://www.merriam-webster.com/dictionary/identity
- https://www.thefreedictionary.com/identity
- https://www.collinsdictionary.com/dictionary/english/identity
- https://www.yourdictionary.com/identity
- https://dictionary.cambridge.org/dictionary/english/identity
- https://en.wiktionary.org/wiki/identityhttps://en.wikipedia.org/wiki/Identity
-
I then found an interesting quote:
G.K. Chesterton once observed that the “special mark of the modern world is not that it is skeptical, but that it is dogmatic without knowing it.” His point was that moderns have forgotten that they are assuming what they believe to be a given. “In short,” he concludes, “they always have an unconscious dogma; and an unconscious dogma is the definition of a prejudice.”
With this thinking in mind on definition stood out:
identity n.
-
-
-
-
- an individual’s sense of self defined by (a) a set of physical, psychological, and interpersonal characteristics that is not wholly shared with any other person and (b) a range of affiliations (e.g., ethnicity) and social roles. Identity involves a sense of continuity, or the feeling that one is the same person today that one was yesterday or last year (despite physical or other changes). Such a sense is derived from one’s body sensations; one’s body image; and the feeling that one’s memories, goals, values, expectations, and beliefs belong to the self. Also called personal identity.
- in cognitive development, awareness that an object is the same even though it may undergo transformations. For example, a coffee cup remains the same object despite differences in distance, size, color, lighting, orientation, and even shape. Also called object identity.
-
-
-
I then thought of the various ways people expand on this word Identity and began to build a list.
-
-
-
- Brand Identity
- Cultural Identity
- Digital Identity
- Ego Identity
- Emotional Identity
- Ethnic Identity
- Family Identity
- Gender Identity
- intellectual Identity
- Material Identity
- Moral Identity
- National Identity
- National Identity
- Official Identity
- Organizational Identity
- Personal Identity
- Physical identity
- Political Identity
- Psychology Identity
- Racial Identity
- Sexual Identity
- Social Identity
- Spatial Identity
- Visual Identity
-
-
I am convinced my list is not complete. What I can say is each item can be found in an article, definition or other written material produced by others.
As a final thought
Understand our identity leads one to wonder
“Who am I”
an Existential question
we each must answer for ourselves
The Identifier should not be the Authenticator
I was asked to look into the value of the EMV Secure Remote Commerce Specifications. In the first section they wrote:
“1.1 Background … While security of payments in the physical terminal environment have improved with the introduction of EMV specifications, there have been no such specifications for the remote commerce environment. …”
This statement caused a bit of angst. It caused me to think of the work to create SET and Visa’s efforts to promote the original version of 3D-Secure. I was further reminded of how difficult it has been to find the balance between convenience and fraud and how merchants are more worried about abandonment than they are about the cost of fraud. Ultimately, it caused me to wonder about the goal of the EMV 3-D Secure specification.
“To reflect current and future market requirements, the payments industry recognised the need to create a new 3-D Secure specification that would support app-based authentication and integration with digital wallets, as well as traditional browser-based e-commerce transactions. This led to the development and publication of the EMV® 3-D Secure – Protocol and Core Functions Specification. The specification takes into account these new payment channels and supports the delivery of industry leading security, performance and user experience.”
The keywords found in the last sentence “the delivery of industry leading security, performance and user experience” suggest these two specifications are searching to solve the same problem.
According to the Oxford dictionary
Security is
- “The state of being free from danger or threat.”
- “Procedures followed or measures taken to ensure the security of a state or organization.”
Authentication is
- “The process or action of proving or showing something to be true, genuine, or valid.”
- “Computing The process or action of verifying the identity of a user or process.“
On this same page, the authors go on to make the following statement
“… there is no common specification to address the functional interactions and transmission of data between the participants.”
This then causes me to wonder about the original ISO 8583 specification, the current ISO 20022 specification, and the subsequent concept of the three-domain model within the 3D-Secure specification. All three of these specifications define the interaction between the participants while not restricting the method of transmitting the data. It seems the authors of the SRC specifications have forgotten history. Or, are they trying to rewrite history.
At this stage, Authentication seems to the most important part of what EMV is attempting to address. But, the focus seems to be more about rewriting history that solving the fundamental problem. We seem to have this desire to take public identifiers and convert them into secrets.
“An industry transition from a dependency on Consumer entry of PAN data can be accomplished by providing an SRC specification that meets the needs of all stakeholders involved.”
These intriguing contradictions beg the question. Why did the authors of the Secure Remote Commerce specification not reference the good work of those that created the 3D-Secure specification and propose an approach unlike EMV? They all are part of the same organization!
Is the goal not to address authentication and Security of the payment transactions, be they instore or on the Internet. I would argue
We allowed the PAN, the payment card identifier, to become a means of authentication
This use of the PAN as both an identifier and an authenticator; reminds me of a hearing of the United States House Committee on Ways and Means May 17th, 2018 hearing on “Securing Americans’ Identities: The Future of the Social Security Number”.
“House Ways and Means Social Security Subcommittee Chairman Sam Johnson (R-TX) announced today that the Subcommittee will hold a hearing entitled “Securing Americans’ Identities: The Future of the Social Security Number.” The hearing will focus on the dangers of the use of the Social Security number (SSN) as both an identifier and authenticator, and examine policy considerations and possible solutions to mitigate the consequences of SSN loss or theft.”
All the witnesses and most of our members of congress accepted and understood the problem. We allowed a simple government-issued identifier to become a means of authentication, in other words, an authenticator. Like allowing the social security number and now also the PAN to become part of how we authentic someone’s identity. We caused these publically available identifiers to become valuable and sensitive PII data.
Cardholder Authentication and Consumer Device Identification
What is clear, as one continues reading the SRC specifications, is the goal is to reduce the frequency of presenting payment credentials on merchant websites.
“Minimising the number of times Consumers enter their Payment Data by enabling consistent identification of the Consumer and/or the Consumer Device”
A very different approach to what the payment schemes do with the EMV based payment process. The authors of EMV saw the PAN as public data, they architected something designed to assure the uniqueness of the card and the ability to positively verify cardholder. Card Authentication and Cardholder Verification.
Why not simply think and focus on the same architecture? Simply change the word “card” to “device” and focus on Device Authentication and Cardholder Verification or as everyone is promoting Multi-Factor Authentication. We simply need to make sure the thing is genuine and the right individual is using the thing. The thing is what the cardholder has – The “what you have” factor. Add a pin/password or better still a biometric to be the second factor the “what you know” or “what you are” factor.
EMV 3D-Secure creates the ability to exploit the “what you have” factor by offering Device fingerprint data to the issuer’s authentication process.
Pay to be Paid
An interesting concern and a telling phrase. When one Googles the phrase “Pay to the Paid” the result takes us into the contracts associated with Protection and Indemnity insurance P&I.
When I entered the search term, I was thinking about how financial institutions see ‘payments’ as a revenue source. In particular, the word ‘Interchange’ springs to mind. I remember sitting in a management meeting in Foster City, at the Visa International offices, as we discussed the results of a McKinsey study this study stated the banks were not earning from their most frequent activity – processing payments.
We then as Visa saw a need to help our members appreciate the breadth and complexity of this simple word “Payment”. Payment Zsars and Gurus were all the rage. International Banks spent millions to create payment factories capable of supporting ACH, WIRE, Swift and card payment. Was the goal to streamline the process? For some, yes! For others, the focus was on reducing costs. For others, they focused on creating a sticky proposition capable of assuring long term relationships with their corporate clientele. For all, increase revenue and profit.
Did any actually think to focus on streamlining the mechanical process of moving money between two individuals or entities? Many will argue yes. Why did they not seek to develop Real-time Gross Settlement Systems, RTGS? Why is it only new economies that saw these opportunities?